FraudLabs Pro assigns a unique identifier (device ID) to each machine that is used to visit an e-commerce site. These machine specific identifiers are stored in the browser cookies. Devices here refer to computers, laptops, tablets and mobile phones. FraudLabs Pro leverages this device ID to track purchases for fraud detection purposes. Read further to learn how to stop fraud using device validation rules.
Installing the FraudLabs Pro Agent JavaScript #
To start collecting device data from webstore visitors, your webpage should include some JavaScript codes in either the header or footer.
- Go to the Developer Guide page.
- Copy the JavaScript code and paste into your webpage header/footer to setup the device validation.
- Once you’ve done the above, the FraudLabsPro plugins for the various opensource e-commerce platforms can start to use the device ID to track and stop fraud using device validation.
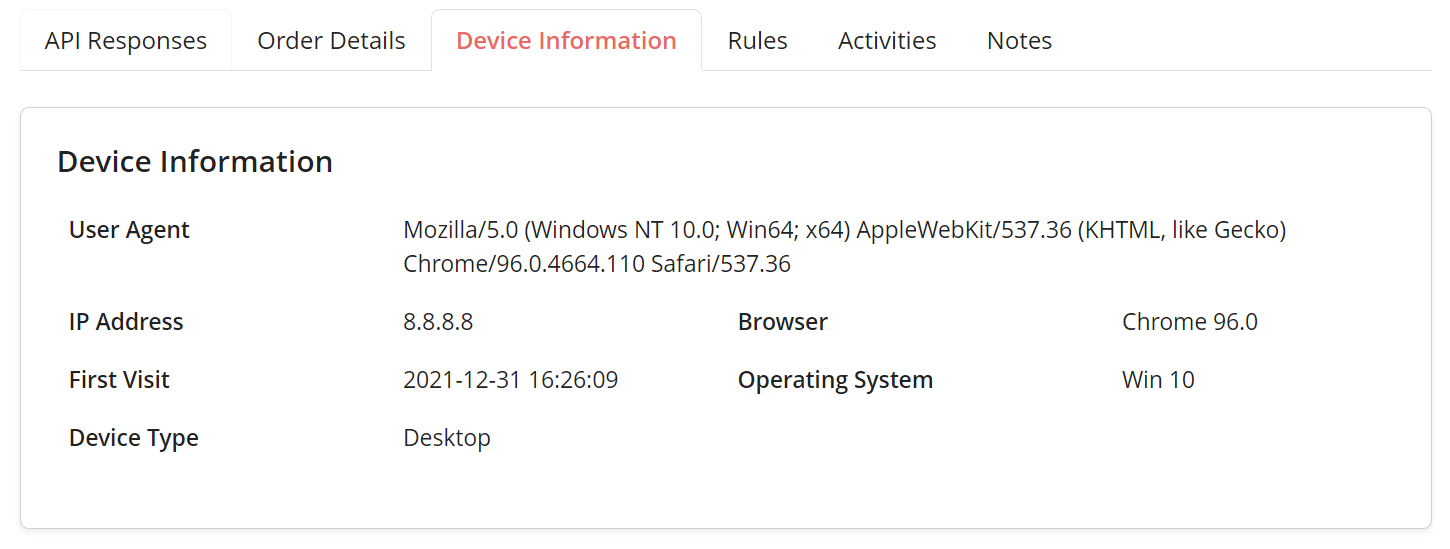
You can login to your Merchant area and view the transaction details for new orders after you’ve setup the above. You should see some data in the Device Information tab like below:
How to stop fraud using device validation rules #
Once you can see that the device data collection is working, then it’s time to take the next step. Go to the Rules page and try adding a new rule. You should see the below list of device validation rules.
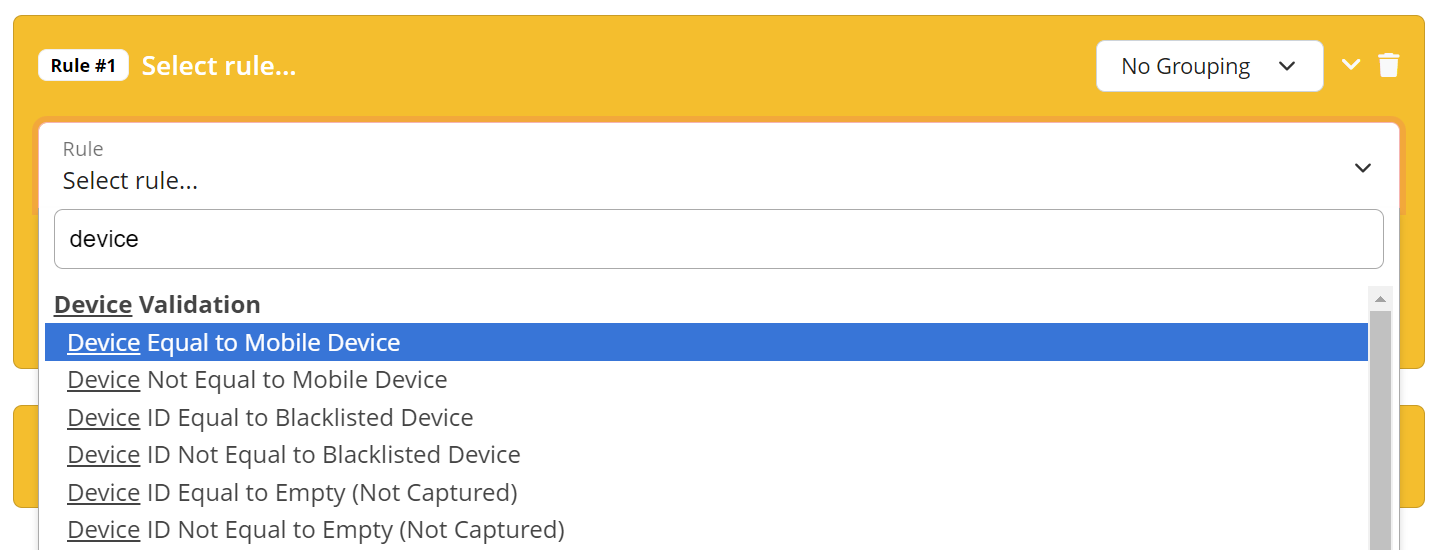
If you wish to flag orders from mobile device for manual review, you can do so with the above rule. Same goes if you wish to automatically reject all orders from blacklisted devices.
There is also a rule for when the user managed to suppress the device data collection. Merchants should utilize this rule to flag such orders for manual review.
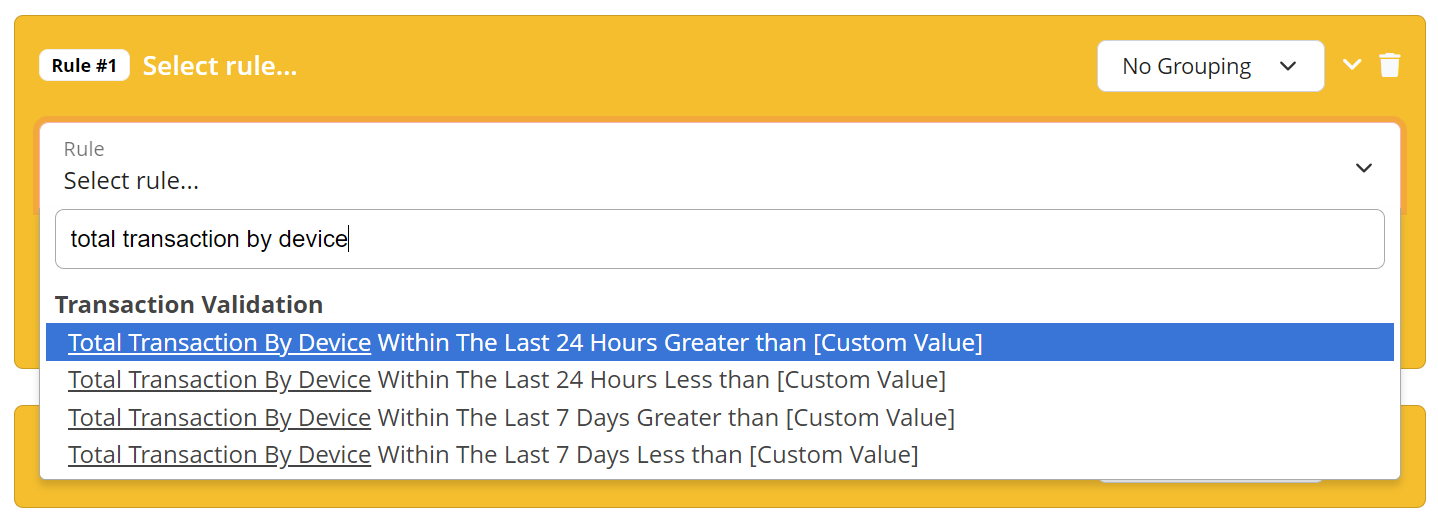
In addition to the mobile and blacklist rules, there are also velocity checks for device validations. As you can see, you have the option to flag orders if the number of transactions by device is greater or less than a specified number. These velocity rules work with either a 7-day period or a 24-hr period. When someone makes a certain number of transactions within the specified period, the rule can either flag the order for review or reject it outright.
Conclusion #
Fraudulent order detection normally works by tracking purchases via IP address or email address. However, fraudsters are now smarter and have learnt to use proxy servers to change their IP address. They also frequently use a lot of different emails from various free providers. Device validation can still detect and stop them from committing order fraud. That said, it is still possible to prevent the device data from being collected, hence, it’s advisable to use the device validation in conjunction with other types of rules.