Hackers never stop to steal. They tend to create new tricks and spread it across the network to infect private computers. These, are called Trojan horse or malware.
There are millions machines infected by malware or Trojan horse. FraudLabs Pro detects and highlights if the IP address has been infected by malware. An exploited machine can be controlled remotely to perform fraud transactions without leaving a trace.
How to prevent sensitive information being spy by malware and protect your browsers against exploit attacks?
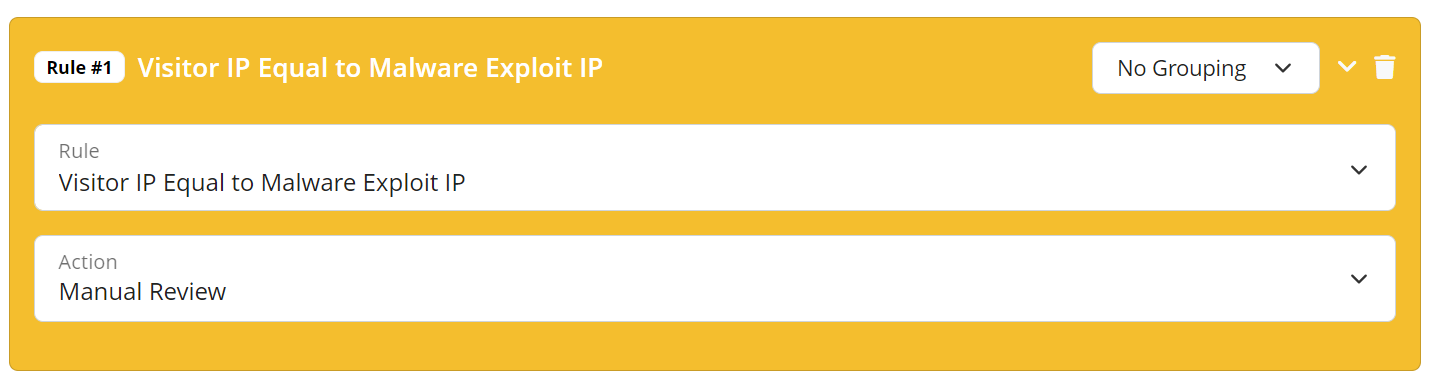
How to configure malware exploit validation? #
Ready to start with FraudLabs Pro? #
Get Micro plan for free, you can quickly explore and integrate with our fraud prevention solution in minutes.