
Device validation is a proven method to identify a user uniquely. It is because this validation helps merchants to unveil one of the common fraud patterns used by fraudsters to disguise themselves as legitimate unique buyers. For instance, the fraudster could use different emails and IP addresses to make multiple purchases. Nevertheless, if the fraudster uses the same device for this malicious activity, then this can be detected by the device validation. This is because the device that is used by the fraudster has been labeled uniquely and that info is stored in the system.
In order to enable the device validation, you will need to include the FraudLabs Pro Agent JavaScript into your website. It can be included either inside the footer file or the checkout page of your website. However, for the WooCommerce platform, you just need to install the FraudLabs Pro for WooCommerce plugin then the JavaScript will be embedded automatically during the installation steps.
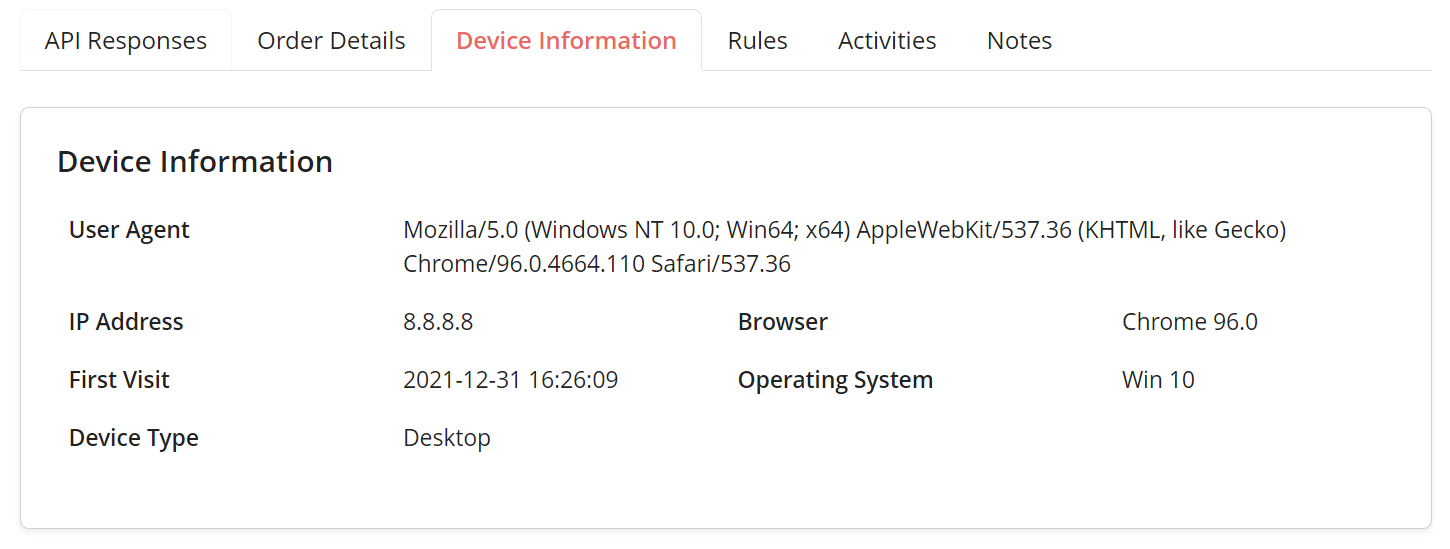
Once you have the device validation enabled, you shall be able to view the device information at the transaction details page. The screenshot below shows an example of the device information.
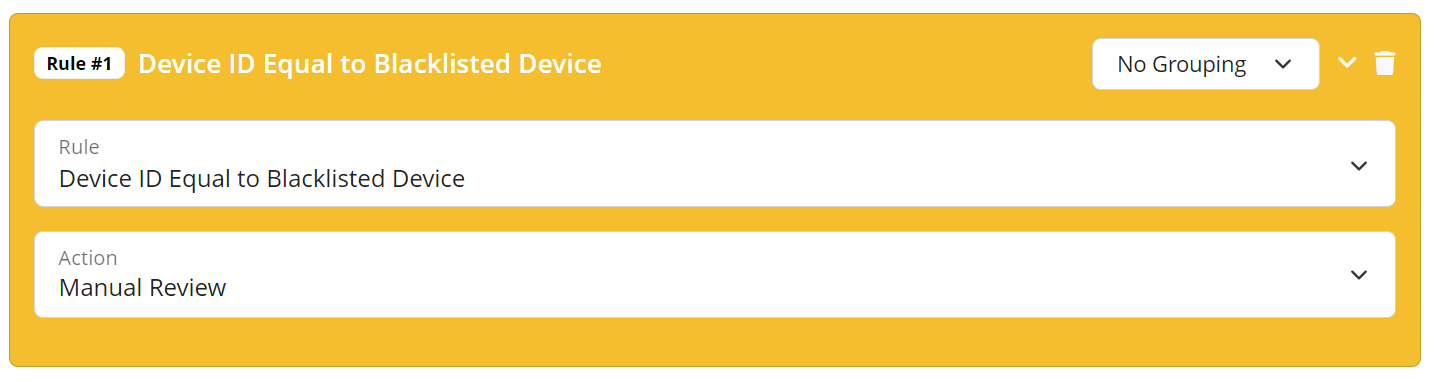
In addition, you can create a device validation rule at the FraudLabs Pro Merchant Rule page to review or reject the order if the device was blacklisted. With the help of device information, you can easily find out if a client’s device had been reported and blacklisted by other merchants in our merchant network. You may blacklist this device for future purchases if any malicious act was discovered during the fraud validation.
In conclusion, device validation is another suggested method that helps merchants to protect their online stores from malicious fraudsters. It can be done by analyzing all order transactions for fraud patterns with the device information captured.
Ready to start with FraudLabs Pro? #
Get Micro plan for free, you can quickly explore and integrate with our fraud prevention solution in minutes.